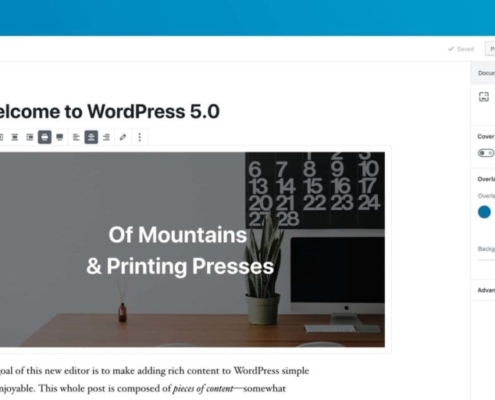
Word up! Tickbox technical director Daryl Phillips explains recent changes to WordPress and Tickbox’s approach to upgrading your site
It’s been a week (or so) since WordPress 5.0 (Bebo) was released. Some of you may have seen, upgraded or received an update notification about it.
It's the biggest update so far for Wordpress. The main focal point centred around the rich…
Goodbye SHA-1, Hello SHA-2
Google Chrome (and similarly FireFox) is deprecating support for SHA-1 before the year is out. So the time to check and upgrade is paramount. All SHA-1 support will be removed by the end of 2016. Your site will continue to be served, but with that unruly error: "Your website is not trusted.".
DirtyCow moooo-ving to a server near you
No you read that right. DirtyCow - or copy-on-write for those inclined - is the latest hidden vulnerability to hit unprotected servers and in some cases Linux driven smartphones.
Looking for paid subjects for user testing workshop
We're holding a user testing workshop for a new site we are launching and are looking for people to take part.
The workshops are being held on Thursday 9th April at our offices in Park Street, Bristol, and testing subjects will receive £15 for taking part.
